Why Cloud Services Are Important for Modern Businesses
Wiki Article
Protect Your Information With Top-Tier Cloud Storage Space Services
In an age where information security is critical, delegating your beneficial information to top-tier cloud storage solutions is a critical relocation for safeguarding versus prospective dangers. These solutions surpass plain storage space, offering cutting-edge encryption methods, strict access controls, and adherence to market criteria. By checking out the nuances of data security within cloud storage space services, you can boost your company's strength to cyber dangers and make certain the durability of your electronic assets.Relevance of Information Security
Executing durable data security gauges helps in preserving confidentiality, stability, and availability of information. File encryption transforms data into a safe and secure style that can only be accessed with the appropriate decryption key, guaranteeing that also if information is intercepted, it remains unreadable to unapproved parties.
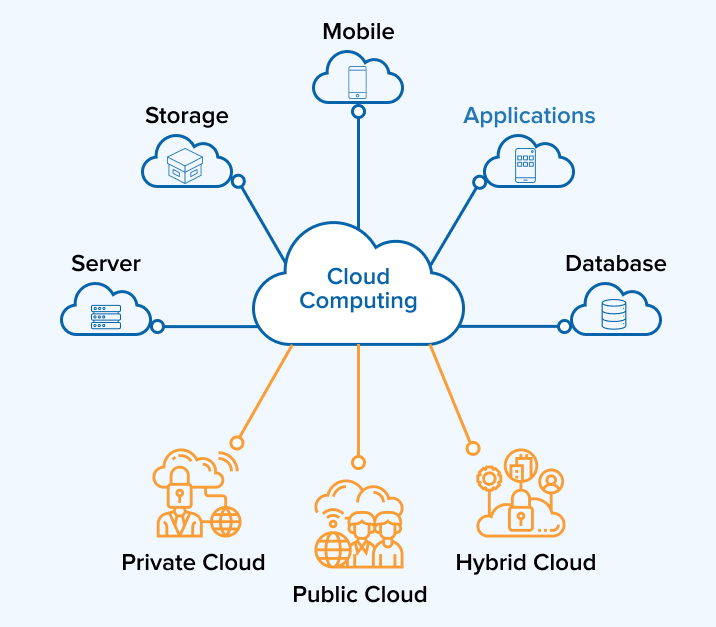
Benefits of Cloud Storage
In today's digital landscape, the use of cloud storage space supplies various benefits for individuals and organizations looking for protected and effective information management options. One vital benefit of cloud storage is its scalability. Users can easily enhance or reduce their storage needs without the problem of physical upgrades or equipment installments. This adaptability enables cost savings and makes sure that storage space ability straightens with existing needs.Individuals can access their data from any kind of location with a web connection, promoting collaboration and remote job abilities. Furthermore, cloud storage supplies improved data protection procedures such as encryption, redundancy, and routine back-ups.
In addition, cloud storage solutions typically feature automatic synchronization throughout devices, making certain that the most updated variation of files is offered in all times. Generally, the benefits of cloud storage make it a beneficial solution for contemporary information administration requires.
Key Functions to Search For
When evaluating top-tier cloud storage space services, it is necessary to consider vital functions that enhance information administration performance and protection. One critical function to try to find is scalability. A durable cloud storage service should supply scalability choices to suit your information development without endangering efficiency. The ability to quickly scale up or down ensures that you only pay for the storage you need, optimizing cost-effectiveness.Another crucial feature is information encryption. Look for a cloud storage space service that supplies end-to-end security to secure your information both in transit and at remainder. Security assists protect your delicate information from unapproved access, guaranteeing information privacy and conformity with regulations.
Look for cloud storage solutions that provide collaboration features like real-time editing and enhancing, documents versioning, and individual approvals manage. Prioritizing these key features will certainly aid you select a top-tier cloud storage solution that satisfies your information administration requires efficiently and safely.
Safety And Security Procedures and Compliance
Making sure robust protection measures and conformity standards is paramount for any top-tier cloud storage space solution supplier in safeguarding delicate data (universal cloud Service). To accomplish this, leading cloud storage services execute a multi-layered method to safety and security. This consists of file encryption methods to shield information both in transportation and at rest, robust access controls to make sure just authorized users can check out or adjust data, and routine safety audits to recognize and deal with any vulnerabilities proactivelyCompliance with sector guidelines such as GDPR, HIPAA, or PCI DSS is also critical for cloud storage space carriers. Complying with these criteria not just aids in securing information yet also constructs trust fund with clients who count on these services to keep their delicate information firmly. In addition, top-tier service providers often go through third-party security accreditations to demonstrate their commitment to maintaining high-security requirements.
Tips for Selecting the Right Solution
Make sure that the storage room fulfills your current needs and allows for scalability as your information grows. Next off, evaluate the solution's reliability and uptime guarantees to decrease prospective downtime and ensure continual access to your information. Think about the degree of protection steps applied by the provider, such as security procedures and data security mechanisms, to safeguard your delicate information.Verdict
Finally, safeguarding data with top-tier cloud storage space solutions is important in making sure the security and integrity of sensitive information. By leveraging robust safety and security actions, file encryption procedures, and compliance requirements, organizations can safeguard their information from cyber threats and information violations. Picking a credible cloud storage supplier that focuses on information defense is important for maintaining discretion and availability while gaining from scalability and enhanced safety attributes in the digital age.With the raising reliance on digital data storage space, the threat of cyber risks and information violations has actually likewise grown.Applying robust information defense measures assists in keeping confidentiality, integrity, and availability cloud services press release of data. Encryption transforms information into a secure format that can just be accessed with the correct decryption secret, making certain that also if data is obstructed, it remains unreadable to unauthorized parties.Making certain durable security steps and conformity requirements is paramount for any top-tier cloud storage space service carrier in protecting delicate information. By leveraging durable safety measures, encryption protocols, and conformity requirements, companies can secure their data from cyber risks and information breaches.
Report this wiki page